Hands-on training to attack and defend Google Cloud environments, from IAM to multi-project infrastructure
Our GCP security training gives your team practical skills to identify and exploit real attack paths across IAM, Compute Engine, GKE, and Cloud Functions. Through hands-on labs in real Google Cloud projects, your engineers will exploit misconfigurations, build detections, and implement defensive controls used by leading security teams.

Exploit and secure GCP IAM bindings, service accounts, and Workload Identity Federation
GCP IAM is uniquely complex, with resource-level policies, organisation-level bindings, and service account impersonation chains that can create subtle but impactful privilege escalation paths. Our hands-on labs walk your team through real attack scenarios targeting IAM misconfigurations, overly permissive service account keys, domain-wide delegation abuse, and Workload Identity Federation trust exploitation. Learners gain practical skills in auditing IAM policies, detecting privilege escalation vectors, and implementing least-privilege architectures across GCP projects and folders.
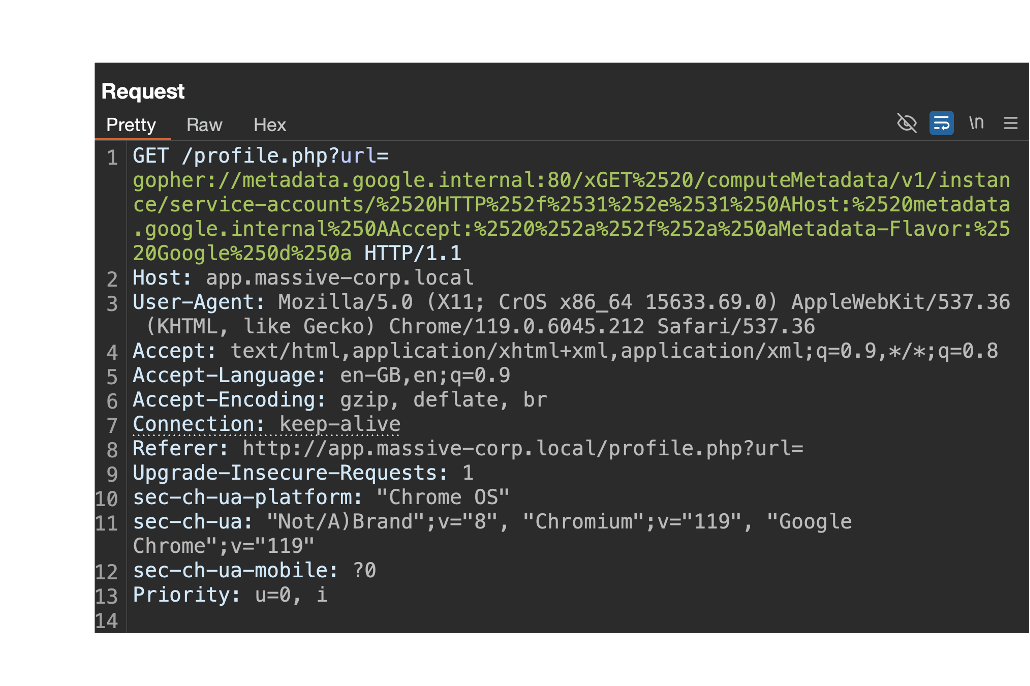
Attack and defend Compute Engine, metadata services, and workload infrastructure
GCP compute infrastructure presents unique attack surfaces through metadata endpoints, service account bindings, and application-level vulnerabilities. Our labs guide your team through real exploitation scenarios including SSRF attacks against the metadata server, privilege escalation via set-metadata and startup scripts, and lateral movement through overly permissive service account configurations. Learners gain practical experience attacking and defending VMs, Cloud Functions, Cloud Run, and CI/CD pipelines, then apply detection and response techniques using GCP-native security tooling across realistic multi-project environments.

Secure Cloud Storage, IAM, service accounts, and GCP compute services
GCP breaches often start with an application vulnerability and escalate through misconfigured IAM. Our hands-on labs walk your team through real attack chains that exploit SSRF, SQL injection, and JWT forgery to gain a foothold, then pivot through overly permissive service accounts, implicit delegation, and HMAC key abuse across Compute Engine, Cloud Functions, Cloud Run, and Cloud SQL. Your team will learn to identify these attack paths and implement the defensive controls to stop them.

Cloud Audit Logs, Security Command Center, and custom detections for threat detection
Effective cloud security requires robust logging, monitoring, and detection capabilities. Our GCP logging and detection labs teach your team to configure and analyse Cloud Audit Logs across Admin Activity, Data Access, and System Event streams. Learners work with Logs Explorer and Log Analytics to investigate real attack patterns, build custom detections from Security Command Center findings, and develop incident response workflows using GCP-native security tooling to detect and respond to threats in real time.

Practitioner-led pentesting from real-world operators
Pwned Labs isn't a traditional consultancy. We're practitioners who build, break, and defend cloud environments every day. Our penetration testers hold certifications including CRT, AWS Security Specialty, AZ-500, and Google Professional Cloud Security Engineer, and actively contribute to the offensive security community through research, tooling, and training content used by thousands of professionals worldwide.
Every engagement is led by operators with direct experience across Fortune 500 environments, startups, and regulated industries. We deliver clear, actionable findings with risk-rated remediation guidance your engineering teams can implement immediately. Our clients return because we find what others miss and communicate it in a way that drives real security improvement.